Happy Ides of March, y’all! I guess that’s a bit of an oxymoron, but it’s fine. While we were all eating sandwiches and pretending to work but looking at houses online, a lot of serious security stories broke. As you can suspect, a lot of them have to do with the Russia/Ukraine stuff.
Thousands of Secret Keys Found in Leaked Samsung Source Code
OOF. From the article: “The firm’s researchers have yet to determine how many of the exposed keys are valid. However, their analysis showed that 90% are likely associated with internal systems and “can be more challenging for an attacker to use.” On the other hand, the remaining keys — roughly 600 of them — can grant attackers access to a wide range of systems and services.” About 10% of those keys are for external services too, like GitHub and AWS. Yikes
German government advises against using Kaspersky antivirus
Well, this is pretty similar to some former warnings about Kaspersky and it’s no surprise. Founder/CEO Eugene Kaspersky raised some ire with a recent tweet about “compromise” in the Russia/Ukraine thing, but that’s also not surprising. They’re in a tough spot: because, as is mentioned in the article, “While Kaspersky is likely trustworthy and ethical, it still has to abide by Russian laws and regulations, including allowing state agents to access private firm databases.” This is reason enough to proceed with caution.
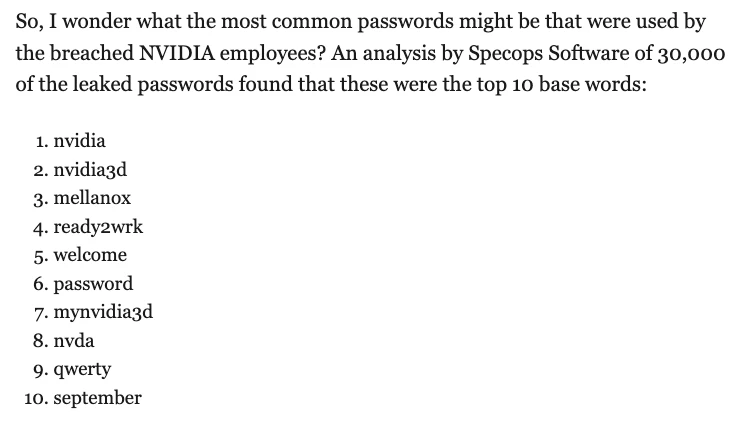
NVIDIA Staff Breached Passwords
And from an intrepid field reporter out in Facepalm City: